When you come across the phrase “ensuring software quality” in the modern software development landscape, it goes far beyond just ensuring functionality and performance. Security has become an essential pillar of quality assurance. One approach to securing your application is penetration testing, or pentesting.
| Key Takeaways: |
|---|
|
This article explores popular penetration testing tools every QA team should know, along with practical insights on integrating them into daily workflows.
What is Penetration Testing?
Penetration testing (or pentesting) is a testing approach in which an authorized, simulated cyber attack is conducted on an application, network, or system to identify vulnerabilities and evaluate an organization’s defenses.
- SQL Injection
- Cross-Site Scripting (XSS)
- Broken authentication and session management
- Security misconfigurations
- Sensitive data exposure
- Insecure APIs
Who are Pentesters?
Penetration testers (pentesters) are security professionals who are skilled in ethical hacking. In fact, the terms “ethical hacking” and “penetration testing” are sometimes used interchangeably, but they differ. Ethical hacking is a broader cybersecurity dimension that encompasses the use of hacking skills to enhance network security. Penetration tests are just one of the methods ethical hackers use.
- Detect common vulnerabilities early
- Automate recurring security checks
- Support security teams with initial findings
- Validate fixes after vulnerabilities are addressed
Why Penetration Testing Matters for QA Teams?
Application security vulnerabilities can have severe consequences, including financial loss, reputational damage, and legal penalties. QA teams play a crucial role in identifying issues before software reaches production to prevent these outcomes.
Penetration testing (pentesting) is crucial for QA teams as security is switched from a reactive, post-production afterthought to a proactive, integrated part of the software development lifecycle (SDLC). It ensures that the application is safe from malicious exploitation, protecting both brand reputation and data.
- Shift-Left Security: Pentesting incorporated early in the SDLC process can detect vulnerabilities that are easier and cheaper to fix. For this, it is integrated with the QA process.
- Proactive Threat Detection: Penetration tests simulate real-world attacks to identify coding errors, misconfigurations, and authorization flaws that automated scanners miss.
- Risk Reduction: QA teams can prevent potential exploitation by attackers by proactively identifying weaknesses.
- Compliance Requirements: Regular penetration testing should be conducted in many regulatory industries, such as finance, healthcare, and retail, for compliance with standards like PCI DSS, HIPAA, and GDPR.
- Improved Product Quality: Pentesting helps ensure the application is secure and high-quality.
What are Pentesting Tools?
Penetration testing tools automate tasks, improve testing efficiency, and help identify issues that are difficult to discover with manual analysis alone. After assessing threats and vulnerabilities, penetration testers submit a report to the organization so that it can address the identified risks to improve its cyber defenses.
Pentesting tools are needed for security testing in modern, large-scale IT environments. Using pentesting tools, testers can evaluate systems against security benchmarks and compliance requirements.
Types of Penetration Testing Tools
A penetration testing toolkit should include a variety of tools. Here are several common types of pentesting tools:
- Port Scanners: They identify open ports on the system. Port scanners are used in reconnaissance and can provide ideas for potential attack vectors.
- Vulnerability Scanners: Known vulnerabilities in servers, operating systems, and applications, as well as misconfigurations that can be exploited in a test, are searched for by vulnerability scanners. Using reports from vulnerability scanners, pentesters can select an exploitable vulnerability that grants them initial access to the system.
- Network Sniffer: This type of tool monitors information in network traffic, including its source, destination, the devices communicating on the network, protocols, and ports used. This information is useful to check if the data is encrypted or identify communication paths that can be used during penetration testing.
- Web Proxy: Testers can intercept and modify traffic between their browser and web server using a web proxy. Testers can detect hidden form fields and other HTML features that might enable attacks like cross-site scripting (XSS) or cross-site request forgery (CSRF).
- Password Cracker: Password crackers help penetration testers determine if an organization’s employees are using weak passwords that might pose a risk of abuse.
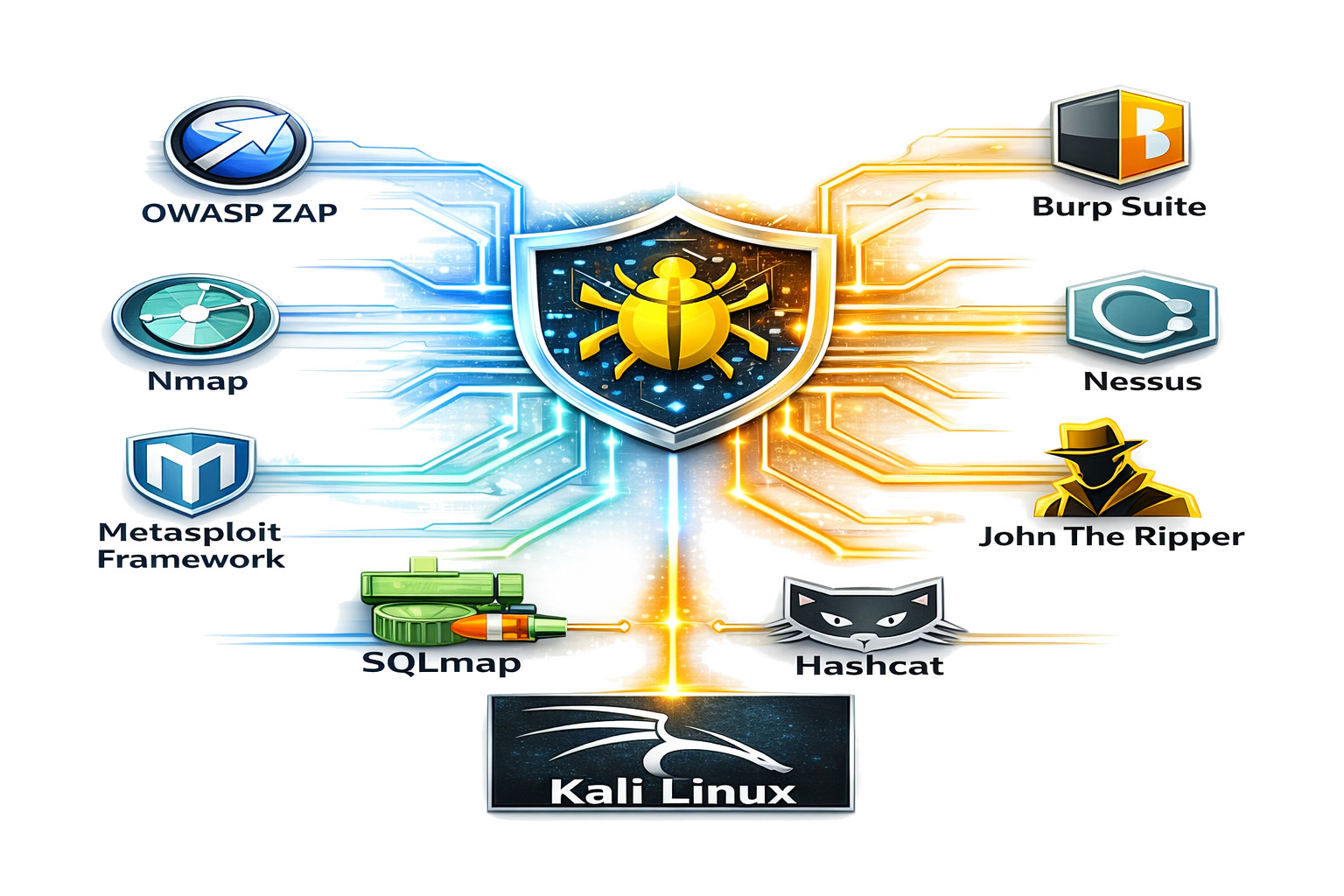
Categories of Penetration Testing Tools
Penetration testing (pentesting) tools are crucial for identifying vulnerabilities such as SQL injection, cross-site scripting (XSS), and misconfigurations before they reach production.
Penetration testing tools are categorized by their primary function and align with the types already discussed. The following table summarizes the various categories of pentesting tools and their examples:
| Category | Examples |
|---|---|
| Web application security scanners (Proxy and interception tools) | OWASP ZAP, Burp Suite |
| Network scanning tools | Nmap, Nessus |
| Exploitation frameworks | Metasploit Framework, SQLMap |
| Password and authentication testing tools | John the Ripper, Hashcat |
| API security testing tools | Postman, SoapUI |
| Cloud and container security tools | Trivy, kube-bench |
| Specialized Security Ecosystems | Kali Linux, BeEF (Browser Exploitation Framework) |
We will discuss each tool in our next sections.
OWASP ZAP (Zed Attack Proxy)
OWASP ZAP is a widely used open-source tool highly suitable for beginners and professionals alike. It is an alternative to Burp Suite and is excellent for integrating security checks into CI/CD pipelines.
- Easy to set up and use
- Automated vulnerability scanning
- Passive and active scanning modes
- API testing capabilities
- Integration with CI/CD pipelines
- Ideal for integrating into automated testing workflows
- Strong community support
Practical Use: QA teams can automatically detect vulnerabilities such as XSS or insecure headers by running ZAP scans during builds.
Burp Suite
Burp Suite is one of the most powerful tools for web application penetration testing and is considered the “industry standard” for web app testing. It offers a free community edition and a professional version.
- Intercepting proxy for modifying requests
- Intruder tool for automated attacks
- Repeater for manual testing
- Advanced scanner (in paid version)
- Provides deep insights into application behavior
- Enables manual testing of complex vulnerabilities
- Helps simulate real attacker techniques
Practical Use: QA engineers can use the tool to test for injection vulnerabilities by intercepting HTTP requests and manipulating parameters.
Nmap (Network Mapper)
This is a powerful open-source, go-to tool for network discovery, security auditing, port scanning, and host identification. It is vital to understand the attack surface and identify which services are exposed on the network.
- Port scanning
- Service detection
- OS fingerprinting
- Scriptable scanning using NSE (Nmap’s Scripting Engine)
- Helps identify exposed services
- Useful for validating infrastructure security
Practical Use: QA teams can use these tools to scan staging environments, ensuring only necessary ports are open.
Nessus
Nessus is a premium, commercial vulnerability scanner known for its comprehensive database of known vulnerabilities. It is trusted by security professionals worldwide to perform credentialed and non-credentialed scans, detecting flaws, misconfigurations, malware, and compliance gaps.
Nessus provides broad coverage across endpoints, virtual machines, and servers, and aligns results with standards such as PCI DSS and HIPAA for enterprise security assurance.
- Extensive vulnerability detection
- Configuration auditing
- Compliance reporting
- Quickly identifies known issues
- Generates detailed, actionable reports
Practical Use: Nessus is primarily used for vulnerability management, compliance auditing, and penetration testing support.
Metasploit Framework
Metasploit is one of the most widely used and versatile penetration testing frameworks. It is used for exploit development, vulnerability assessment, and post-exploitation analysis. It has over 2100 exploits, using which testers can simulate advanced threats and validate system defenses.
- Large database of exploits
- Payload generation
- Post-exploitation capabilities
- Confirms the real impact of vulnerabilities
- Helps prioritize issues based on risk
Practical Use: QA teams can use Metasploit to test the exploitability of a vulnerability in a controlled environment.
SQLmap
SQLmap is a powerful open-source tool that automates the detection and exploitation of SQL injection vulnerabilities. It supports multiple database engines and attack techniques, enabling full database takeover to demonstrate the true impact of a flaw.
- Database fingerprinting
- Accessing an underlying file system
- Over data fetching from a database
- Executing commands on an operating system using out-of-band connections.
Practical Use: QA teams can use SQLmap to set up automatic recognition of various password hash formats and processes for cracking them using a dictionary-based attack.
John the Ripper
John the Ripper is a free password cracking tool that supports many operating systems. The tool is customizable and provides multiple options for password testing.
- Auto-detection of password hash types.
- Wide support for encrypted password formats, including Unix crypt hashes, Kerberos AFS tokens, and Windows LAN Manager (LM) hashes.
- Ability to crack password encryption based on DES, MD5, Blowfish, and MD4.
- Support for password hashes and passwords stored in databases and directory systems such as LDAP and MySQL.
Practical Use: John the Ripper helps system administrators find weak (easy to guess or crack via brute-force) passwords.
Hashcat
Hashcat is a popular password cracker capable of cracking highly complex representations. It combines multiple highly effective password cracking methods.
- Identifies a hash that matches a discovered password hash and cracks the password.
- Manipulates hash keys generated by MD5, SHA, WHIRLPOOL, RipeMD, NTMLv1, and NTMLv2 algorithms.
- Converts readable data to a hashed state
- Supports a variety of methods, including dictionaries, rainbow tables, and brute force techniques
Practical Use: Penetration testers can use Hashcat to uncover compromised and easy-to-guess credentials in a certain environment.
Postman (with Security Testing)
Postman is a widely used and versatile tool for API development, and beginners may find it valuable for API penetration testing. Testers can interact directly with API endpoints, manipulate requests, and identify vulnerabilities.
- It is a customizable API client
- Automated testing
- Acts as a Postbot AI agent
- API documentation generation
Practical Use: The Postman tool is primarily used to validate authentication mechanisms, test input validation, and automate API test scenarios.
SoapUI
SoapUI provides built-in security testing features that let you scan for common vulnerabilities in both SOAP and REST services.
- SQL injection testing
- Boundary and fuzz testing
- API vulnerability detection
- Combines functional and security testing in one tool
Practical Use: SoapUI is extensively used for API mocking/simulation, performance testing, security testing, and functional testing.
Trivy
Trivy is a modern tool and is used for scanning container images and file systems for vulnerabilities.
- Detects OS and library vulnerabilities
- Fast and easy to integrate
Practical Use: Utilized for container image scanning, CI/CD pipeline security (DevSecOps), and IaC scanning.
kube-bench
Designed for Kubernetes environments, kube-bench is a security auditing tool that validates a Kubernetes cluster’s configuration against established security benchmarks.
- CIS Benchmark Compliance
- Comprehensive scanning of work components
- Automation-Ready with JSON output formatting
- Flexible Deployment
Practical Use: Used for automated CIS compliance audits, CI/CD pipeline integration scanning, and vulnerability remediation.
Kali Linux
Kali Linux is an operating system that facilitates penetration testing, security forensics, and related activities. It is an open source Linux distribution based on Debian, maintained by Offensive Security.
| Tool | Purpose |
|---|---|
| Armitage | graphical network attack management tool |
| Nmap | port scanner |
| Wireshark | packet analyzer |
| Metasploit | penetration testing framework with thousands of exploit modules |
| John the Ripper | password cracker |
| Sqlmap | automated SQL injection and database import |
| Aircrack-ng | software suite for wireless LAN penetration testing |
| OWASP ZAP | web application security scanner |
| Burp Suite | application security testing |
Practical Use: Kali Linux is used by QA teams to simulate attacks, analyze web applications (Burp Suite & OWASP ZAP), and exploit vulnerabilities to identify security risks (Metasploit).
BeEF (Browser Exploitation Framework)
BeEF is an open-source penetration testing tool. It is used to evaluate the security posture of a target environment by focusing on client-side attack vectors, specifically the web browser.
- Browser Hooking
- Modular Command Library
- Advanced Command & Control (C2)
- Cross-Origin Attacks
- Automated Rule Engine (ARE)
Practical Use: QA teams use the BeEF tool to test for cross-site scripting (XSS).
Challenges QA Teams May Face
QA teams may face various challenges when using pentest tools:
- Lack of Security Expertise: QA teams may lack adequate security expertise, resulting in violations of regulations.
- Tool Complexity: It may be difficult to acquire tool knowledge, and the team may find it difficult to use the tool.
- False Positives: Automated tools often flag non-existent vulnerabilities (false positives) or, worse, miss critical vulnerabilities (false negatives).
- Integration Issues: It is challenging to keep security testing synchronized with rapid code releases as modern CI/CD pipelines move faster than comprehensive penetration tests.
Best Practices for QA-led Penetration Testing
- Follow the OWASP Top 10 guidelines
- Test in safe, non-production environments
- Record findings clearly and prioritize based on risk
- Continuously upskill and update tools and knowledge
- Incorporate security into test cases
The Future of Penetration Testing in QA
DevSecOps practices are increasingly being adopted in QA, and the role of QA in security testing is evolving rapidly.
- Continuous security testing in CI/CD pipelines
- Vulnerability detection with the help of AI
- Increased focus on API and cloud security
QA engineers with security testing experience will be highly valuable going forward.
Conclusion
Penetration testing techniques are no longer limited to security teams. QA teams are increasingly playing a proactive role in penetration testing by identifying vulnerabilities and ensuring application security.
QA teams can detect vulnerabilities using penetration testing tools such as OWASP ZAP, Burp Suite, Nmap, Metasploit, and Trivy. Detecting vulnerabilities earlier reduces risks and improves overall product quality.
Starting small, tools can be integrated gradually, and a strong security mindset can be built into the QA process. After all, in today’s digital world, delivering high-quality software means delivering secure software, and QA teams are at the forefront of making that happen.
Frequently Asked Questions (FAQs)
- What is penetration testing in the context of QA?
Penetration testing, also known as pentesting, simulates cyberattacks on applications to identify security vulnerabilities before they become threats. QA teams use it to ensure software security.
- Is penetration testing only for security experts?
Not necessarily. QA teams can also perform penetration testing using tools such as OWASP ZAP, though advanced testing requires expertise.
- How can QA teams integrate penetration testing into CI/CD pipelines?
Penetration testing tools like OWASP ZAP or Trivy can be integrated into CI/CD pipelines. They automatically scan applications during builds and deployments, ensuring continuous security testing.
- Are penetration testing tools safe to use in production?
No. Penetration testing tools can disrupt systems or cause unintended damage. Hence, most penetration testing should be conducted in staging or controlled environments.
- Do QA engineers need coding skills for penetration testing?
Not thorough skills, but basic scripting and understanding of HTTP requests, APIs, and application logic are helpful. However, many tools also provide user-friendly interfaces that reduce the need for deep coding knowledge.