If you are someone already in the web security or ethical hacking field, or someone researching it, you would have definitely come across the term Burp Suite.
Burp or Burp Suite is a popular tool mentioned by the majority, and it often feels overwhelming. The tool is used for penetration testing of web applications. Built by Dafydd Stuttard, the tool is owned by PortSwigger. Burp Suite aims to be an all-in-one set of tools, and its features can be improved by installing add-ons (these are called BApps). The tool has an extensive toolkit, which includes Proxy, Intruder, and Decoder.
Burp Suite has a simple point-and-click interface, which makes the process easy, fast, and efficient. The tool is suitable for both freshers and experienced testers. Regardless of whether the goal is to improve the website’s defenses or catch security flaws, the tool makes the entire process more effective.
| Key Takeaways: |
|---|
|
What is Burp Suite?
It is a set of robust security tools for securing web applications and testing. It is trusted by bug bounty hunters and penetration testers across the world. Burp Suite helps catch website vulnerabilities (such as SQL injection attacks and cross-site scripting), and the skillset is enhanced with BApps.
While there are other free tools, such as OWASP ZAP, Burp has a higher popularity due to its intuitive interface and advanced features.
How does it Work?
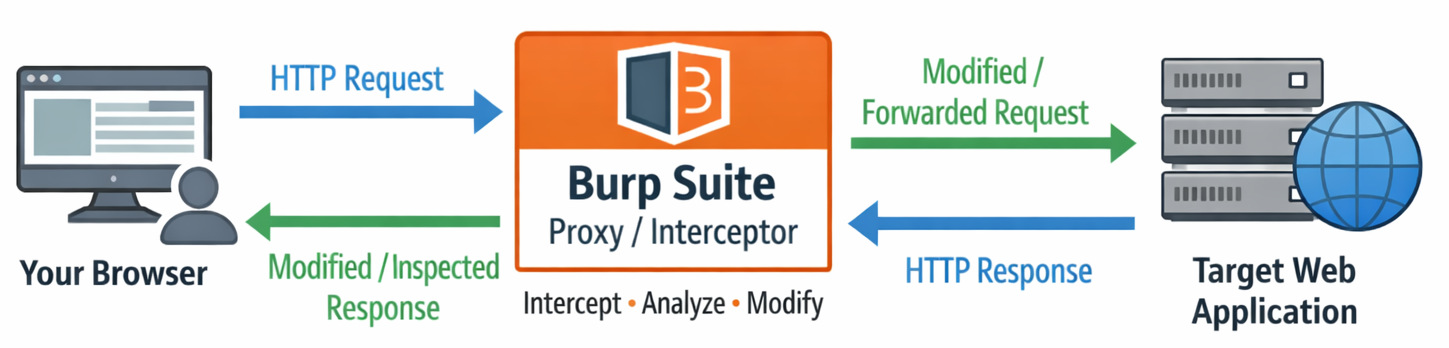
Burp works as a proxy server, placed between your browser and the target web application. This setup allows it to intercept and analyze the HTTP requests and responses. With this advantage, the tool detects vulnerabilities before the attackers can exploit them.
The tool offers detailed reporting capabilities and vulnerability scanning. The detailed reports are helpful to understand the source of the issue and guide you on how to solve the problem. There is a set of 8 tools that help Burp Suite in vulnerability scanning.
Read: SAST vs. DAST Tools: Key Differences Explained.
Burp Suite Tools
Let’s take a look at the main tools in the suite and how they are useful in penetration testing.
Spider
It is a web spider/crawler that crawls through the website to map the application structure. It identifies the main endpoints (i.e., the key pages) on the site. When you analyze more areas for weakness, the more endpoints you find. This helps in pinpointing potential vulnerabilities during the testing stage.
Proxy
The Proxy tool lets users view and change the contents of requests and responses. This is while they are still in transit between your browser and the website. It is useful as it allows you to transmit the intercepted data to other Burp Suite tools for extended analysis. The proxy server can then be adjusted to execute on a specific loop-back IP and a port. In addition, it allows for traffic filtering to concentrate on specific types of responses or requests, simplifying the testing process.
Intruder
- Running dictionary attacks on vulnerable fields such as password forms and fields that are susceptible to XSS or SQL injection.
- Brute force attacks on PINs or passwords
- Validating rate-limiting by sending multiple requests fast.
By observing the website responses to the different inputs, it becomes easier to catch security defects that otherwise would have been missed.
Repeater
- Check if the user-inputted values are being verified.
- How well is the verification being done?
- What values were expected by the server in an input parameter/request header?
- In case of unexpected inputs, how does the server handle them?
- Does the server undergo input sanitation?
- How well were the user-supplied inputs sanitized by the server?
- The server is using which type of sanitation style?
- Which is the actual session cookie among all the cookies available?
- Is CSRF protection being implemented, and can we bypass it?
Sequencer
This is an entropy validator that checks for the randomness of the tokens generated by the web server. Ideally, the tokens should be unpredictable to avoid attacks such as session hijacking since the tokens are normally used for authentication in sensitive operations, such as anti-CSRF tokens and cookies. The randomness should be achieved both character-wise and bit-wise. The entropy analyzer verifies this hypothesis to check the authenticity. Sequencer helps identify weak tokens that can be exploited.
Decoder
This tool lists the common encoding methods, such as HTML, Base64, URL, Hex, etc. It is very useful when you need to understand hidden data in web requests, such as headers or parameters. In addition, Decoder is used for the construction of payloads in attacks such as session hijacking or IDOR (Insecure Direct Object References).
Extender
This tool is useful to attach external components (BApps). These function as browser extensions and increase the Burp Suite functionality. Some BApps are available in the free version, but others require the paid Professional Edition. The Extender window simplifies the management of these external add-ons.
Scanner
The Scanner is not available in the Community edition. It automatically scans websites for common vulnerabilities such as SQL injection and XSS. It gets updated on a regular basis to include new and lesser-known vulnerabilities.
Why is it Necessary for Web Security Testing?
Modern web applications manage sensitive data, which necessitates security testing. Even minor vulnerabilities can lead to serious risks if left ignored. Burp Suite helps testers dig deeper and understand how applications actually communicate.
Requests and responses are analyzed in detail to detect hidden anomalies. This makes it easier to catch common issues like XSS or SQL injection.
Additionally, it helps in mapping the application, making sure that critical endpoints are not overlooked during testing. The testing process is made more structured and efficient in the presence of such tools.
What are the Different Uses of Burp Suite?
It is mainly used for penetration testing. But its use goes beyond that. It helps testers to replicate real-world attacks by changing requests and observing responses.
Attack scenarios are simulated in a controlled environment for testing purposes. It is also leveraged for authentication testing, session management, and catching vulnerabilities in input handling.
Manual testing is another important use, especially for finding complicated vulnerabilities that automated tools might miss. Burp Suite helps testers analyze, test, and improve web application security effectively.
Advantages of Burp Suite
- Faster Pen Testing: Uses the AI-driven features, advanced automation, and specialized extensions. This reduces the time spent catching and exploiting vulnerabilities.
- Comprehensive Scanning: It is a one-in-all platform for scanning, intercepting, and manipulating web traffic. This enables cybersecurity professionals to catch vulnerabilities like XSS, SQL injection, and insecure authentication efficiently.
- DevOps & CI/CD Integration: Integrate Burp Suite with CI/CD and DevOps pipelines to automate application security testing dynamically, allowing security tests.
- Customizable and Extensibility: API-driven plugins like Python, Kotlin, and Java help with higher customization and extensibility. It allows testers to customize functionality to unique testing scenarios and adapt to emerging threats.
Possible Limitations of Burp Suite
- Complex Onboarding: Burp Suite can feel complex in the beginning. The interface isn’t always intuitive, and there’s a lot to take in. Most people feel that way at first.
- Needs Expertise: A high level of expertise may be needed for using each aspect of the Suite efficiently.
- Not Open-source: Also, some of the more powerful features, like the Scanner, are part of the paid version. So, if you’re using the free edition, you might feel a bit limited.
- Slow scans: The highest-level scans can be quite time-consuming.
Example
Imagine you are testing a login form for vulnerabilities using the free Community Edition.
You may want to check for issues like SQL injection or broken authentication. However, since the automated Scanner is not available, you would need to manually intercept requests using the Proxy and test them one by one using tools like Repeater or Intruder.
The testing process is slowed down when automation is not available.
This can be time-consuming, especially if the application has multiple input fields or endpoints. In contrast, the Professional version could scan these areas automatically and highlight potential issues much faster.
Final Thoughts
The suite is an indispensable tool for cybersecurity. The good features make it a popular choice amongst security teams. Actually investing time and effort in learning the tool can help in increasing your security and make sure of a secure digital environment.
Frequently Asked Questions (FAQs)
Is Burp Suite free or paid?
A: It has three versions: Community Edition (Free), Professional Edition(Paid), and Enterprise Edition (Paid).
Which language is used in Burp Suite?
A: It is primarily programmed in Java. Therefore, it functions efficiently and reliably for web security testing.
Does Burp Suite only work for web applications?
A: Burp Suite is mainly designed for testing web applications and APIs. It is commonly used for websites, web portals, and modern applications that communicate over HTTP/HTTPS.